Similar to Canvas fingerprinting, AudioContext fingerprinting is a type of browser or device fingerprinting technique that is relatively new when it comes to device fingerprint elements. By utilizing the AudioContext API in modern browsers, one can exploit the subtle differences in the rendering of a fixed audio waveform, for example a sine or triangle wave, to extract a consistent fingerprint. It should be noted that when using the AudioContext API to fingerprint a system, the code does not collect sound played or recorded by your machine - an AudioContext fingerprint is a property of your machine's audio stack itself.
This technique received media coverage in 2016 after the publication of the research paper "Online Tracking: A 1-million-site Measurement and Analysis" by Steven Englehardt and Arvind Narayanan at Princeton University.
In a study of 18,000 machines, the AudioContext device fingerprint was resulting in approximately 5.4 bits of entropy, however it's beleived that the entropy would be higher in a larger data set. It may also be possible to optimize the input data to improve entropy further.
How It Works
There are two common methods in the wild to fingerprint the audio stack, they are slightly different in their approach but both are equally effective.
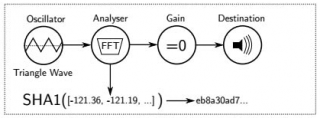
The graphic above shows the use of the AudioContext property to device fingerprint the audio stack. First, a triangle wave is generated using an OscillatorNode. This signal is passed through an AnalyserNode and a ScriptProcessorNode. Finally, the signal is passed into a through a GainNode with gain set to zero to mute any output before being connect to the AudioContext destination (e.g. the computer speakers). The AnalyserNode provides access to a Fast Fourier Transform (FFT) of the audio signal, which is captured using the onaudioprocess event handler added by the ScriptProcessorNode. The resulting FFT is fed into a hash and used as a fingerprint.
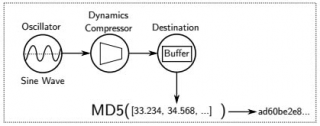
The graphic above shows the use of the OfflineAudioContext property to device fingerprint the audio stack. First, a sine wave is generated using an OscillatorNode. The output signal is connected to a DynamicsCompressorNode, in order to increase differences in processed audio between systems. The output of this compressor is passed to the buffer of an OfflineAudioContext. A hash of the sum of values from the buffer is then used as a fingerprint.
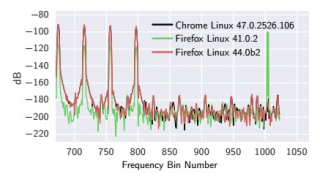
Below you can see a visualization of the processed OscillatorNode from a test fingerprinting script. It's clear there is enough variation to use this function as a device fingerprint.
Further research needs to be done to determine if either method described above is significantly better, and if a sine, square, sawtooth, triangle wave or custom wave provides better fingerprinting.
Entropy Estimate: 8.1 bits
Code
The javascript function below fingerprints the browser languages. You may also download this code here: TBD
Code
TBD |
Validation
Unlike other code on the Internet we do everything possible to verify our code for you. In order to minimize problems and maximize compatibility this code has been verified with JSLint and has been extensively tested with over 1100 OS/Browser combinations using BrowserStack.
Reference
Online tracking:A 1-million-site measurement and analysis (n.d.). In Princeton Web Census. Retrieved September 01, 2017, from http://randomwalker.info/publications/OpenWPM_1_million_site_tracking_measurement.pdf